In this article, we will use Kleopatra software to encrypt and decrypt data. If you want to know more about asymmetric cryptography, you can read this article. For the purpose of this article, knowledge about cryptography is not needed.
To install Kleopatra, visit the page below and proceed with installation.
https://gpg4win.org/thanks-for-download.html
Kleopatra will be installed along other components of GPG4Win software.
.
1. Creating key
- To create a new key pair, open Kleopatra and click "New Key Pair" as displayed below.

- A new window will open asking for:
• Your name
• Your email address
- To protect your key with password, check the "Protect the generated key with a passphrase" box.
- When done, click on "Advanced Settings"

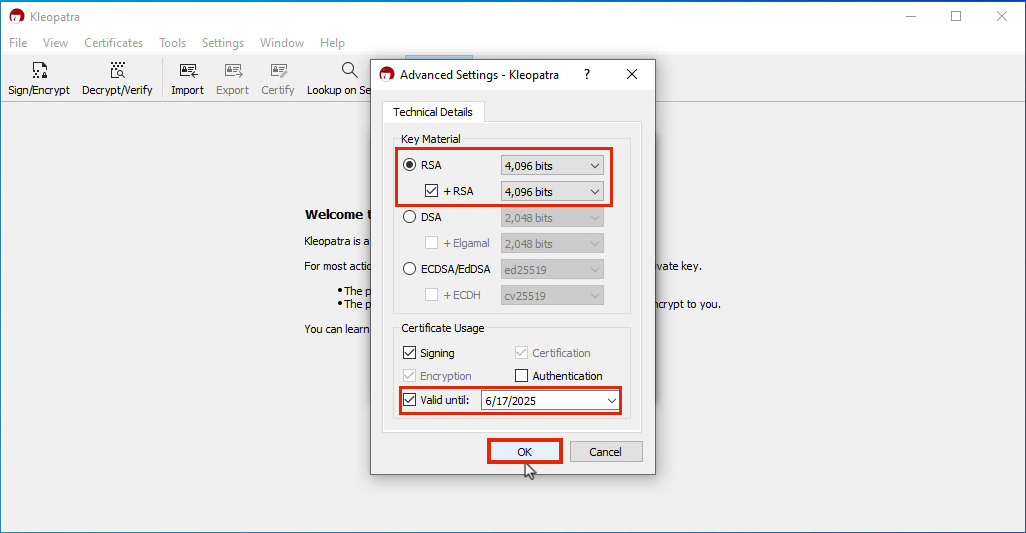
As shown in the image below, choose "RSA" as the encryption algorithm with key length of 4096 bytes.
- You can choose an expiration date for your key in front of "Valid until" check box. It is recommended to set an expiration date that is in 2 years.
A new window will open asking for the password you want to set for you keys. You will need to type it twice to make sure you have not mistyped it.
It is recommended to choose a complex password consisting of uppercase/lowercase letters, numbers and special characters such as !, @, $, etc. You also need to make sure it cannot be guessed.

When done, click "OK".
2. Exporting public key
To receive encrypted files, you will need to share your public key with the sender so they can encrypt the files using your public key. Files encrypted with your public key can only be decrypted by you since you are the only one with private keys. For more details you can refer to the assymetric encryption article.
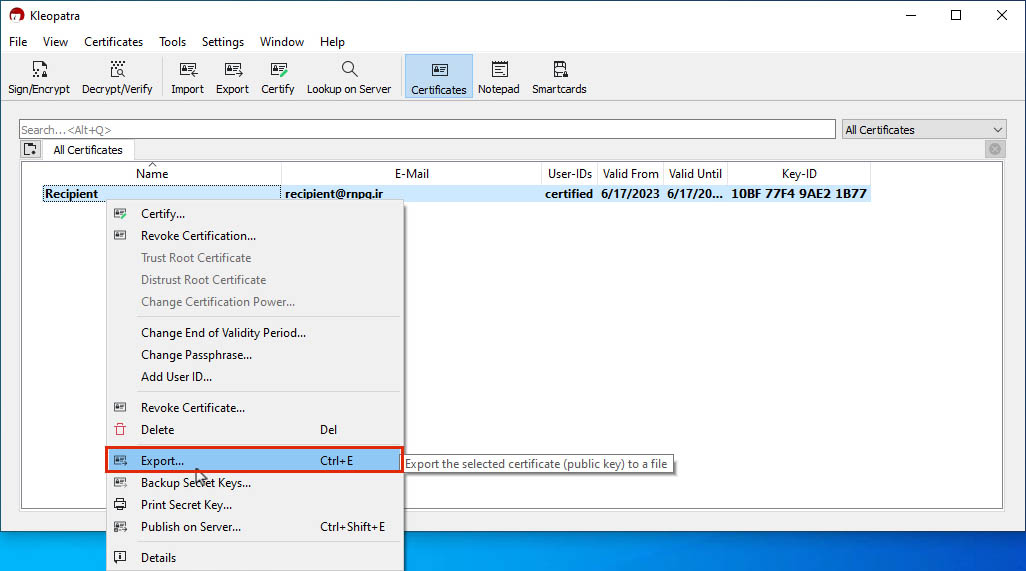
To get your public key, right click on the key you created on Kleopatra and select "Export" as shown below:
Then, choose where you want to save your public key and click "Save".
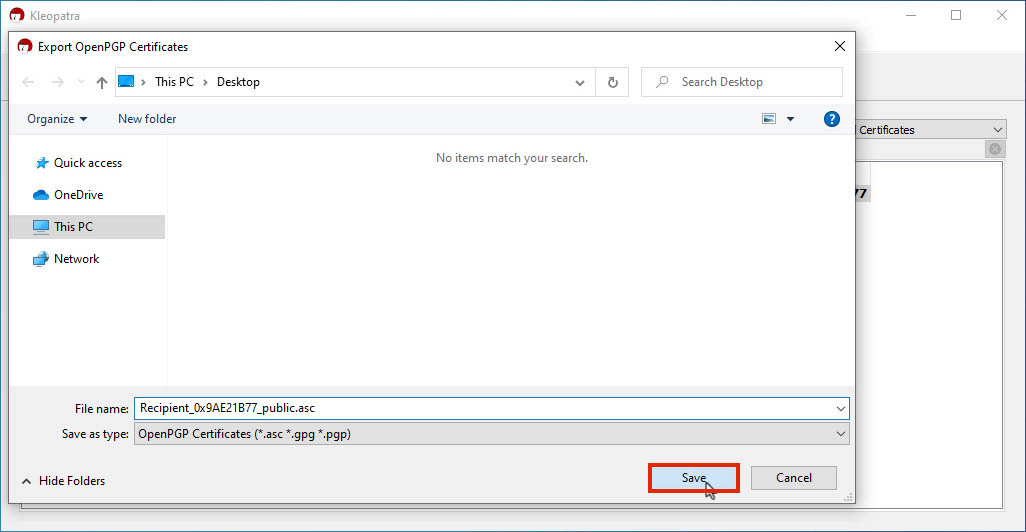
The file you saved can be sent to others so they can encrypt confidential data.
3. Importing public key
As described above, in order to encrypt confidential data, the sender will need to encrypt it using the recipient's public key.
If you want to encrypt files, you will need to import the recipient's public keys to Kleopatra to start using them.
To import keys, click on "Import" button on Kleopatra as shown below:

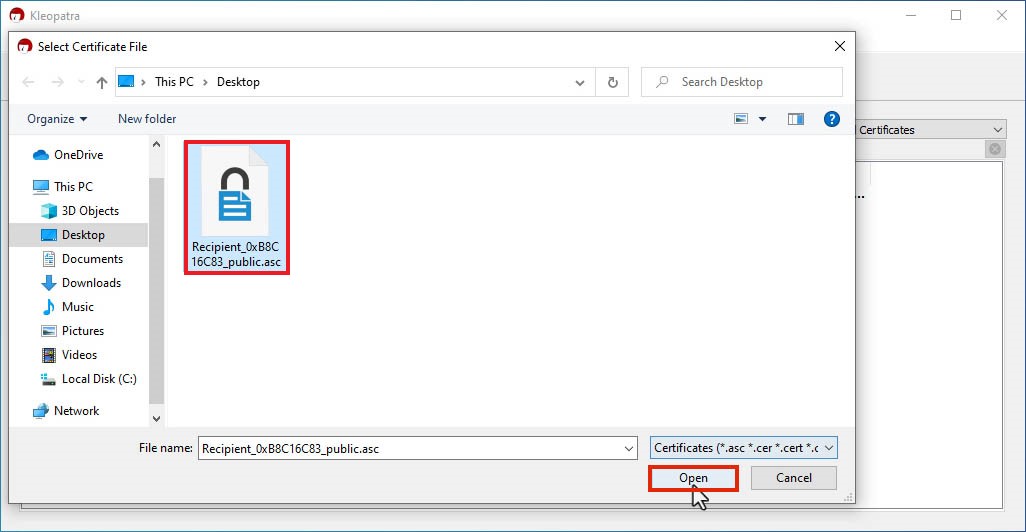
Then, as shown below, select the public key you want to import and click "Open".
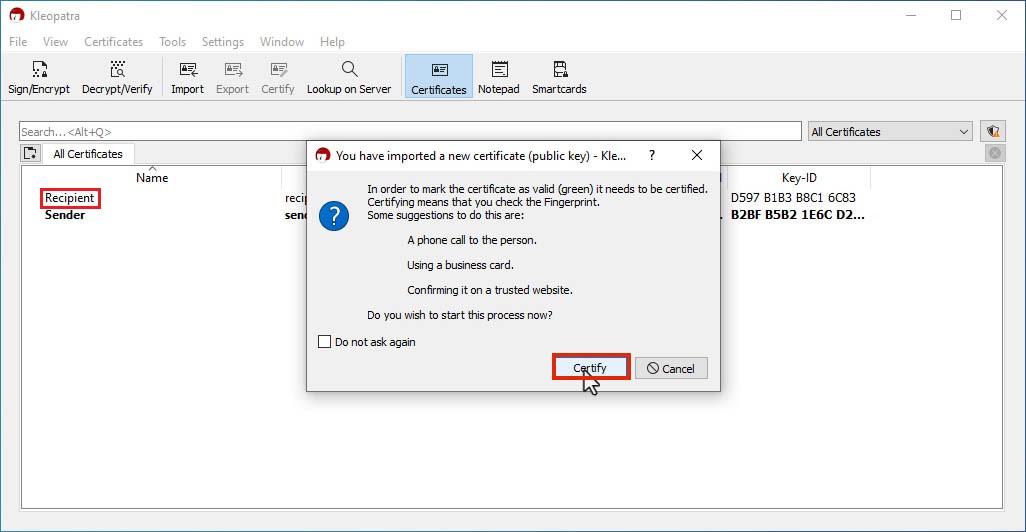
As it can be seen , you need to verify and certify the public keys. To continue, click "Certify"
In case you don't see the certification window as shown below, you can certify it later by right clicking on it and choosing "Certify" option.
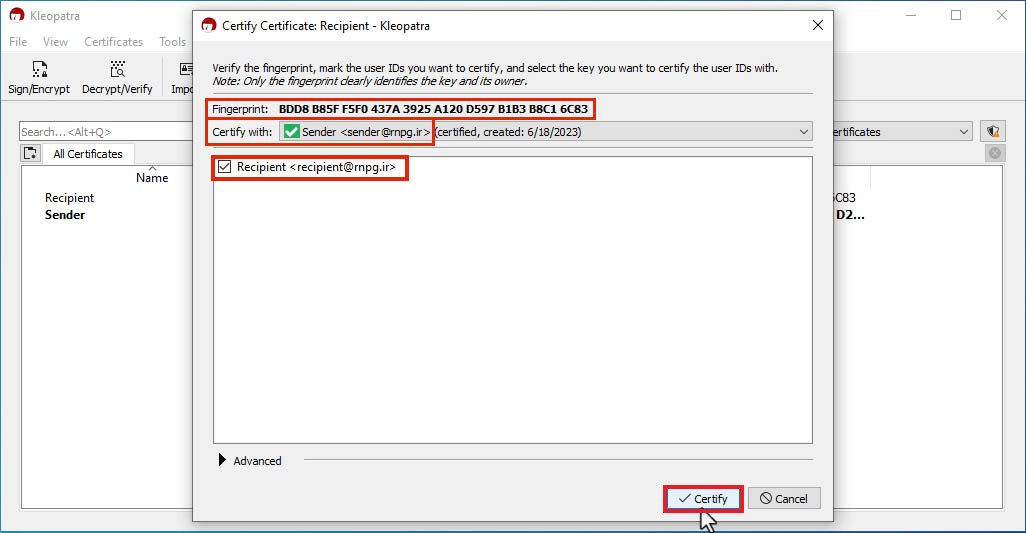
In order to certify a key, you should choose which key you want to certify it with. In front of "Certify with| there is a box that you can choose your key.
You should verify that the value displayed in front of "Fingerprint" is same as the fingerprint of the recipient's key. You can use other means of communication (phone, WhatsApp, etc.) to verify this.
After verification, check the box beside the name of recipient and click "Certify" as shown below.
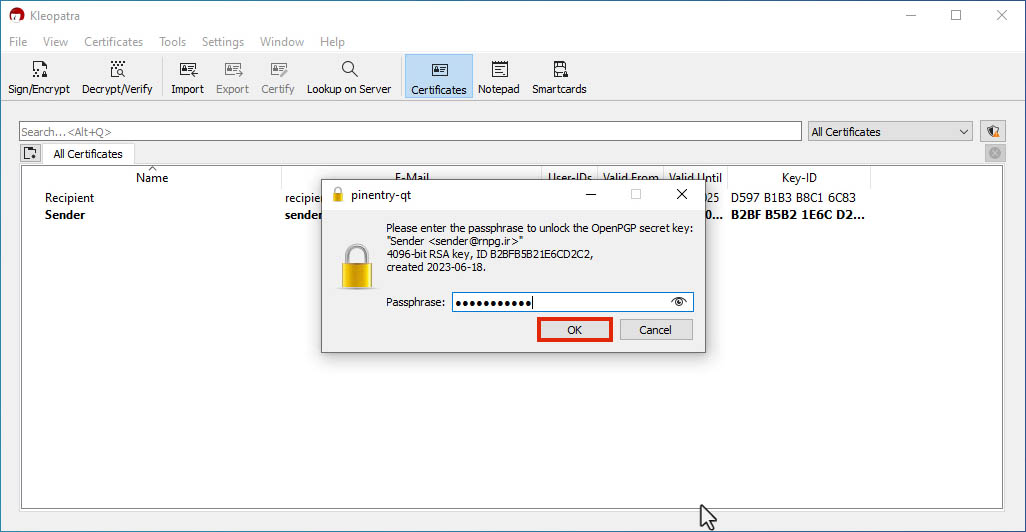
At the end, enter your password and click "OK".
You will not be asked for your password if you have already entered it recently.
After getting the success message, click "OK"

4. Encrypting data
To encrypt confidential data/files, open Kleopatra and click "Sing/Encrypt" as seen below:

Choose the file you want to encrypt and click "Open".

Then, to choose which keys will be used to encrypt the file, click the button as shown below:
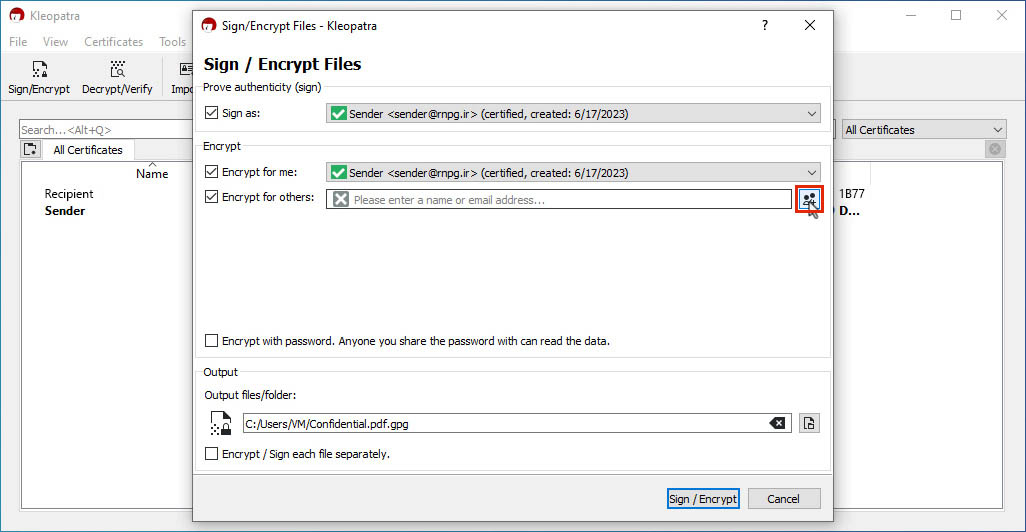
On the list displayed, choose the key you want to encrypt with, which is usually the recipient's key. Then click "OK".

If asked, enter your password and click "OK".
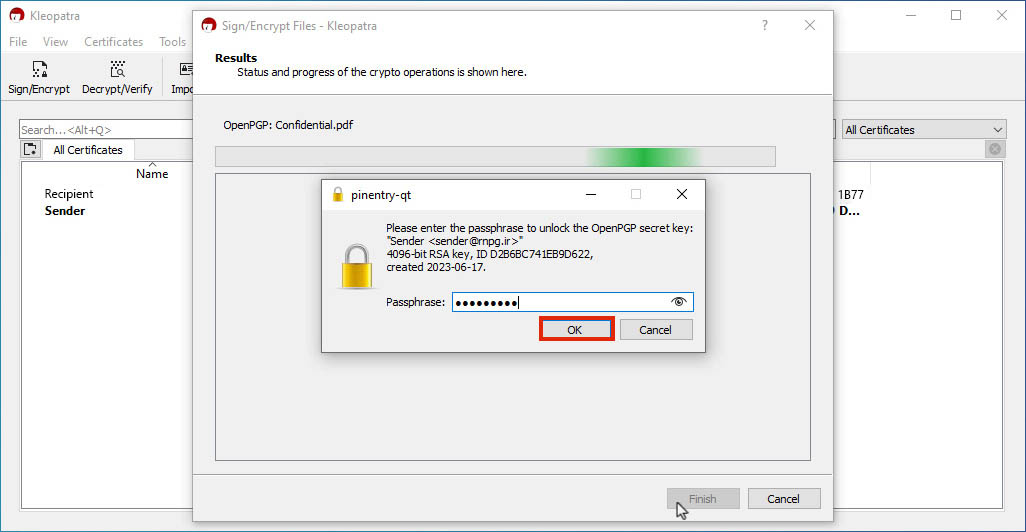
After getting the completion message, click "Finish" .
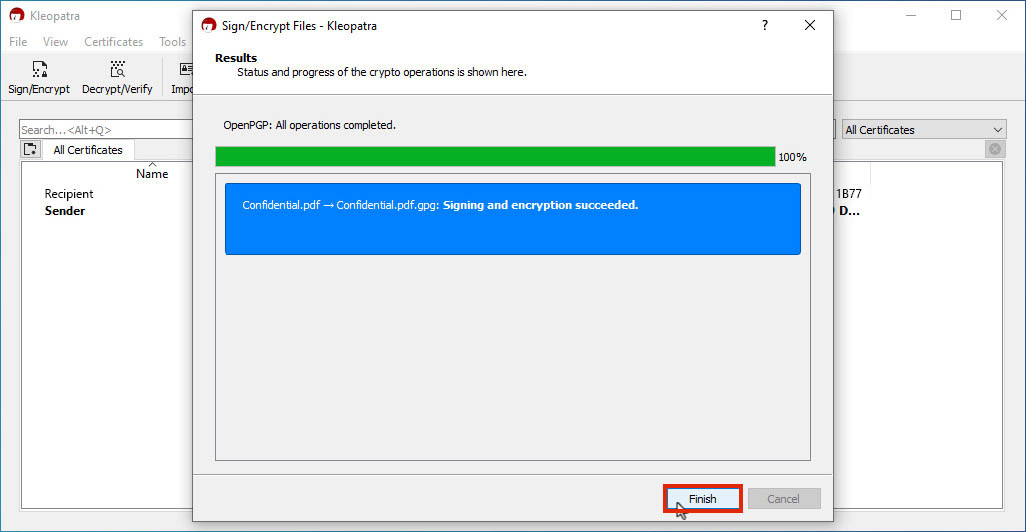
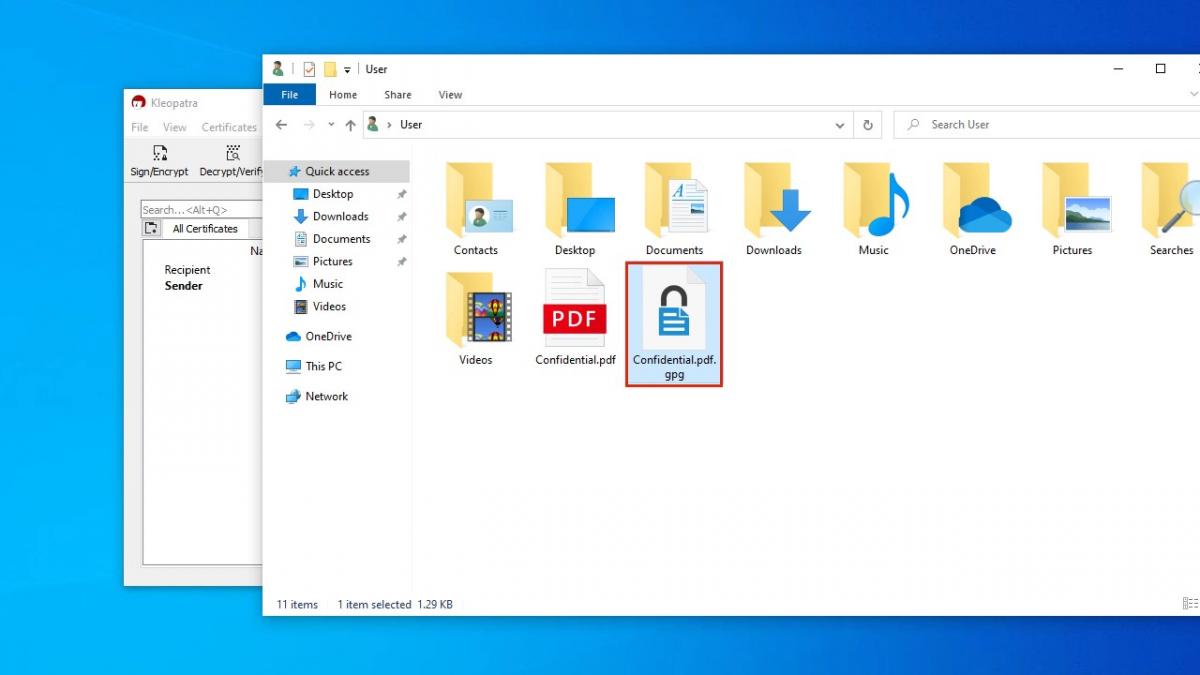
The encrypted file will be created at the same location as the original file with the extension "gpg".
You can now use the encrypted file to securely transfer confidential information.
5. Decrypting data
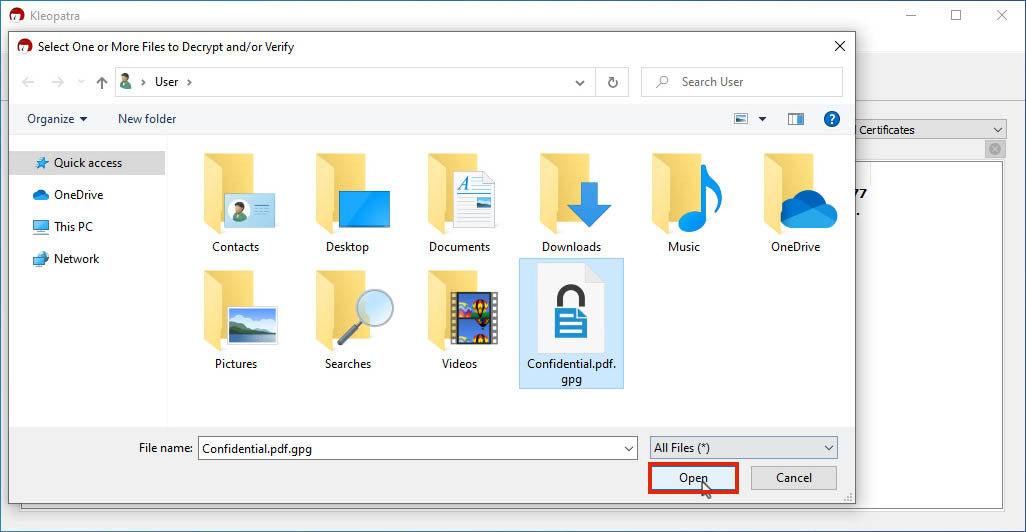
To encrypt a file, click "Decrypt/Verify" as shown below:

Choose the encrypted file and click "Open"
When asked, enter your password and click "OK".
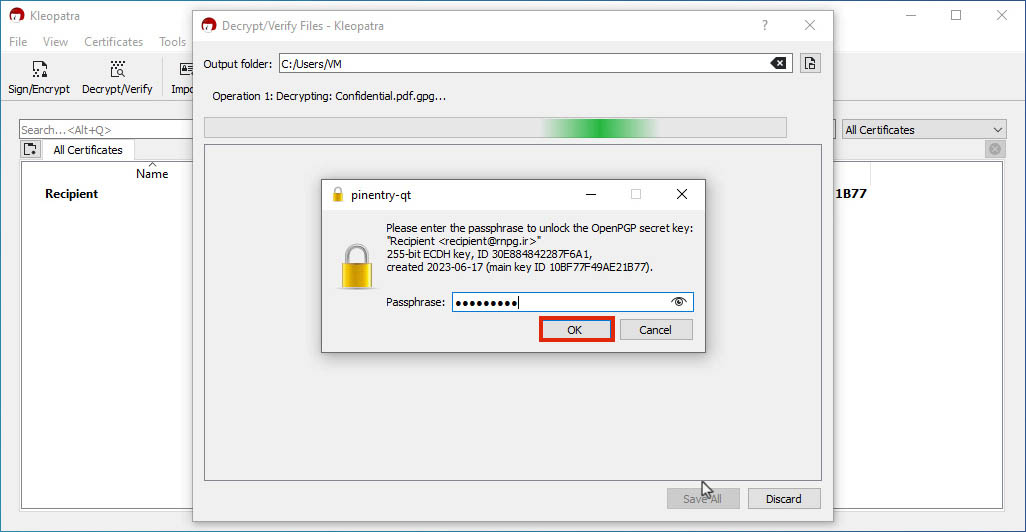
Finally, click "Save All".

The decrypted file will be created at the same location as the encrypted file.



